Unveiling the Blueprint for Cybersecurity: Pattern and Security Requirements

5 out of 5
| Language | : | English |
| File size | : | 18344 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 499 pages |
In the ever-evolving landscape of cybersecurity, organizations face an unrelenting barrage of threats. To effectively combat these challenges, it is imperative to establish a robust foundation of security requirements that guide the design, implementation, and maintenance of secure IT infrastructure. Pattern and Security Requirements, a seminal work by John Steven, offers a comprehensive blueprint for understanding and implementing these essential requirements.
Patterns for Secure Design
Pattern and Security Requirements introduces a framework of security design patterns, which serve as proven solutions to common security challenges. These patterns encompass a wide range of areas, including authentication, authorization, data protection, network security, and incident response. By leveraging these patterns, organizations can effectively address security vulnerabilities and enhance their overall security posture.
One of the key benefits of using design patterns is their ability to facilitate knowledge transfer within security teams. By providing a common language and understanding of security best practices, patterns enable organizations to streamline their security design processes and ensure consistency in their implementation.
Establishing Security Requirements
Pattern and Security Requirements goes beyond design patterns by providing a systematic approach to establishing security requirements. The book guides organizations through the process of identifying, analyzing, and prioritizing security risks, ensuring that their security requirements are tailored to their specific needs and objectives.
The book also emphasizes the importance of traceability, ensuring that each security requirement can be linked back to the specific risks it addresses. This traceability provides a clear audit trail and facilitates ongoing compliance with security standards and regulations.
Implementing and Maintaining Security
Pattern and Security Requirements not only provides guidance on designing and establishing security requirements but also covers their implementation and maintenance. The book discusses best practices for deploying security controls, monitoring and auditing security systems, and responding to security incidents.
One of the key challenges in implementing security requirements is ensuring that they are continuously updated to address new threats and vulnerabilities. Pattern and Security Requirements provides a framework for managing security requirements over time, including processes for reviewing, updating, and communicating changes.
Case Studies and Real-World Examples
Throughout the book, Pattern and Security Requirements draws on real-world examples and case studies to illustrate the practical application of security design patterns and requirements. These examples provide valuable insights into how organizations have successfully implemented effective security measures.
The book also discusses common pitfalls and challenges in implementing security requirements, empowering organizations to learn from the experiences of others and avoid potential roadblocks.
Pattern and Security Requirements is an indispensable guide for organizations seeking to establish and maintain a robust cybersecurity posture. By providing a comprehensive framework for designing, implementing, and managing security requirements, the book empowers organizations to proactively address threats and protect their critical assets.
Whether you are a security professional, an IT manager, or an organization leader, Pattern and Security Requirements is an essential resource that will help you navigate the complex world of cybersecurity and ensure the security of your organization.
5 out of 5
| Language | : | English |
| File size | : | 18344 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 499 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Dan M Frangopol
Dan M Frangopol Casey Winterburn
Casey Winterburn Christopher Clarke
Christopher Clarke David Ronka
David Ronka Ronda Rich
Ronda Rich Jackie J Torell
Jackie J Torell George Lizos
George Lizos Larry Kahaner
Larry Kahaner Nicholas A Yanes
Nicholas A Yanes Steven Quay
Steven Quay Eddie Snipes
Eddie Snipes Abdul Azim Islahi
Abdul Azim Islahi Lisa Gardner
Lisa Gardner Linda M Merriman
Linda M Merriman Leonard B Glick
Leonard B Glick Lucia Raatma
Lucia Raatma Francis Michael
Francis Michael Eli J Finkel
Eli J Finkel Emory Green
Emory Green William Lane Craig
William Lane Craig
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 James GrayAdvanced Computational Algorithms and Material Modelling in Solid Mechanics:...
James GrayAdvanced Computational Algorithms and Material Modelling in Solid Mechanics:...
 Hunter Mitchell99 Juice Smoothie Recipes to Boost Your Health, Cleanse Your Body, and Lose...
Hunter Mitchell99 Juice Smoothie Recipes to Boost Your Health, Cleanse Your Body, and Lose... Douglas AdamsFollow ·18.7k
Douglas AdamsFollow ·18.7k Evan HayesFollow ·6.5k
Evan HayesFollow ·6.5k Felix CarterFollow ·4.9k
Felix CarterFollow ·4.9k Darrell PowellFollow ·5.1k
Darrell PowellFollow ·5.1k Kelly BlairFollow ·10.4k
Kelly BlairFollow ·10.4k Percy Bysshe ShelleyFollow ·9.1k
Percy Bysshe ShelleyFollow ·9.1k Marc FosterFollow ·13k
Marc FosterFollow ·13k Dawson ReedFollow ·16.7k
Dawson ReedFollow ·16.7k
 Ashton Reed
Ashton ReedUnveiling the Silent Pandemic: Bacterial Infections and...
Bacterial infections represent...
 Brent Foster
Brent FosterFinally, Outcome Measurement Strategies Anyone Can...
In today's...
 Brett Simmons
Brett SimmonsUnlocking the Secrets to Entrepreneurial Excellence:...
Empowering...
 Eugene Powell
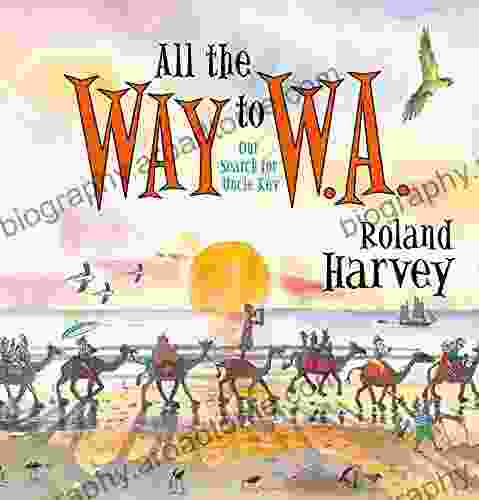
Eugene PowellOur Search For Uncle Kev: An Unforgettable Journey...
Prepare to be captivated by...
5 out of 5
| Language | : | English |
| File size | : | 18344 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 499 pages |