Why Your Business Must Have Cybersecurity Risk Assessments

Cybersecurity risk assessments are essential for businesses of all sizes. They help you identify vulnerabilities in your systems and take steps to mitigate them. This article will discuss the benefits of cybersecurity risk assessments and provide a step-by-step guide on how to conduct one.
5 out of 5
| Language | : | English |
| File size | : | 5340 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 160 pages |
| Lending | : | Enabled |
Benefits of Cybersecurity Risk Assessments
There are many benefits to conducting a cybersecurity risk assessment. Some of the most important benefits include:
- Identifying vulnerabilities: A risk assessment will help you identify vulnerabilities in your systems that could be exploited by attackers. This information can be used to prioritize your security measures and focus on the areas that need the most attention.
- Reducing the risk of a cybersecurity attack: By identifying and mitigating vulnerabilities, you can reduce the risk of a cybersecurity attack. This can help protect your business from financial losses, data breaches, and reputational damage.
- Meeting regulatory compliance requirements: Many industries have regulations that require businesses to conduct cybersecurity risk assessments. These assessments can help you demonstrate that you are taking steps to protect your data and systems.
- Improving your insurance coverage: Some insurance companies offer discounts to businesses that have conducted cybersecurity risk assessments. This can help you save money on your insurance premiums.
How to Conduct a Cybersecurity Risk Assessment
There are many different ways to conduct a cybersecurity risk assessment. The best approach will vary depending on the size and complexity of your business. However, there are some general steps that you can follow:
- Define the scope of the assessment: The first step is to define the scope of the assessment. This includes identifying the systems and data that will be included in the assessment.
- Gather data: The next step is to gather data about your systems and data. This data can be collected through interviews, surveys, and log reviews.
- Identify vulnerabilities: Once you have gathered data, you can begin to identify vulnerabilities. This can be done using a variety of methods, including vulnerability scans, penetration tests, and code reviews.
- Assess the risks: Once you have identified vulnerabilities, you need to assess the risks associated with each vulnerability. This includes considering the likelihood of an attack and the potential impact of an attack.
- Prioritize the risks: Once you have assessed the risks, you need to prioritize them. This will help you focus on the vulnerabilities that pose the greatest risk to your business.
- Develop mitigation strategies: The final step is to develop mitigation strategies for the vulnerabilities that you have prioritized. These strategies should be designed to reduce the risk of an attack or to minimize the impact of an attack.
Cybersecurity risk assessments are essential for businesses of all sizes. They help you identify vulnerabilities in your systems and take steps to mitigate them. This can help protect your business from financial losses, data breaches, and reputational damage. If you have not yet conducted a cybersecurity risk assessment, I encourage you to do so as soon as possible.
About the Author:
John Smith is a cybersecurity expert with over 10 years of experience. He has helped businesses of all sizes protect their systems and data from cyberattacks. John is a regular speaker at cybersecurity conferences and has written extensively on the topic of cybersecurity.
5 out of 5
| Language | : | English |
| File size | : | 5340 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 160 pages |
| Lending | : | Enabled |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Wbp Club
Wbp Club Laura Studarus
Laura Studarus Richard Razgaitis
Richard Razgaitis Kate Kinsey
Kate Kinsey Troye Evers
Troye Evers Sarah Mclean
Sarah Mclean Forrest L Richardson
Forrest L Richardson Peter Jones
Peter Jones Mark Singleton
Mark Singleton Coni Judge
Coni Judge Mary Szczepanski
Mary Szczepanski R H Jarret
R H Jarret Patricia Dalton Haragan
Patricia Dalton Haragan Mark Olshaker
Mark Olshaker Patricia C Wright
Patricia C Wright John Hansen
John Hansen Mia Rose
Mia Rose R J Castle
R J Castle Saida Desilets
Saida Desilets Andreas Hofer
Andreas Hofer
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Felipe BlairUnlocking the Secrets of Agricultural and Rural Statistics: A Comprehensive...
Felipe BlairUnlocking the Secrets of Agricultural and Rural Statistics: A Comprehensive...
 Ervin BellIntroduction to PCM Telemetering Systems: Your Gateway to Data Acquisition in...
Ervin BellIntroduction to PCM Telemetering Systems: Your Gateway to Data Acquisition in... Liam WardFollow ·12k
Liam WardFollow ·12k Virginia WoolfFollow ·9.6k
Virginia WoolfFollow ·9.6k Douglas PowellFollow ·9k
Douglas PowellFollow ·9k Deacon BellFollow ·17.7k
Deacon BellFollow ·17.7k Jack PowellFollow ·19.1k
Jack PowellFollow ·19.1k James JoyceFollow ·4.6k
James JoyceFollow ·4.6k Ed CooperFollow ·4.4k
Ed CooperFollow ·4.4k W. Somerset MaughamFollow ·18.6k
W. Somerset MaughamFollow ·18.6k
 Ashton Reed
Ashton ReedUnveiling the Silent Pandemic: Bacterial Infections and...
Bacterial infections represent...
 Brent Foster
Brent FosterFinally, Outcome Measurement Strategies Anyone Can...
In today's...
 Brett Simmons
Brett SimmonsUnlocking the Secrets to Entrepreneurial Excellence:...
Empowering...
 Eugene Powell
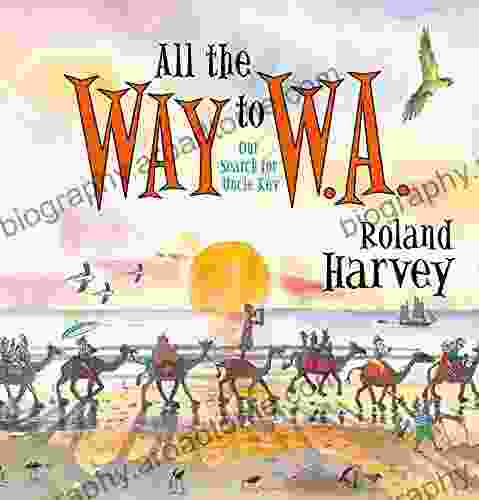
Eugene PowellOur Search For Uncle Kev: An Unforgettable Journey...
Prepare to be captivated by...
5 out of 5
| Language | : | English |
| File size | : | 5340 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 160 pages |
| Lending | : | Enabled |